How IT roadmapping can bring your tech under control
Few people would disagree that planning is a worthwhile activity. Yet, look around ...
How a non-profit overhauled its IT to create a collaborative environment
For the past three years, our team at Smart Dolphins has been working ...

How to enable your team to do more in the cloud
Today's evolving workforce expects mobility, flexibility, and modern technology that unchains them from ...
How Microsoft 365 empowers users to do more and better
Ask any productive team how they do it and, chances are, they will ...

Making the move to cloud accounting
Lots of companies see the value of migrating to the cloud and would ...

How to navigate the paradigm shift of better IT
For decades, IT departments used to be treated as something purely functional or, ...

Business continuity when you still need that server
Now that there is a viable cloud alternative for just about everything, there ...

Strategic Planning and IT Strategy
Strategy and a proper strategic planning process helps you “eat the elephant” one ...
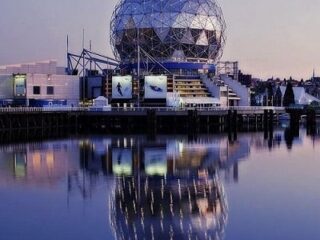
Smart Dolphins IT is servicing Greater Vancouver
Smart Dolphins IT has started servicing businesses located in the Greater Vancouver area ...

Microsoft Teams: why adopt guest and external access
Due to the health restrictions related to the coronavirus pandemic, the businesses community ...

Level up your Microsoft 365 skills
Technical employee empowerment For decades the average professional has been able to get ...